There’s quite a few situations where you may need to run Active Directory Management tools like Active Directory Users and Computers with different credentials. For example:
- Computer is not joined to the domain
- Need to connect to another domain/forest
- Logged in as a standard domain user and need to supply different credentials
- etc…
Step 1 – Install Remote Server Administration Tools (RSAT)
If you are using a 2008 or 2012 WIndows member server, RSAT is a feature you must enable using the directions below:
If you’re using Windows Vista, WIndows 7, Windows 8, or Windows 10 you must download, install, and enable the RSAT feature. Here are the links to download RSAT:
RSAT Windows 10 (By default all features are enabled)
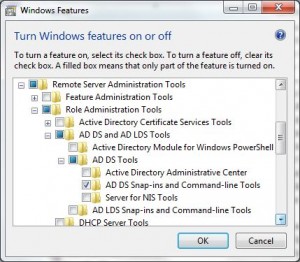
Once you’ve installed RSAT you need to enable the feature (Except Windows 10). Open Control Panel, click Programs and Features, and click Turn Windows features on or off. Then enable the following:
Step 2 – Make Sure You’re on the Domain Network
Make sure you’re on the same network as the Domain Controller. This simply means, connect to the LAN they’re on, or connect to a VPN if you’re remote.
Step 3 – Run As Commands for AD Management Tools
The key to running AD Management tools is the Runas command in Windows, which allows you to specify alternate credentials. However, there are a few gotcha’s with runas such as needing to specify the /netonly command when on a non-domain computer. Here are the commands you’ll need to run to successfully launch the AD Management tools, and all will work whether or not the computer is joined to a domain:
- C:\Windows\System32\runas.exe – Default path to runas
- /netonly – Credentials are specified for remote access, which is required for computers not joined to a domain but still works if the computer is on the domain
- /user: – specify the username by the samaccountname(DOMAIN\user) or UPN(user@domain.local)
- “mmc %SystemRoot%\system32\snapin.msc” – Microsoft Management Console with the path to the snapin.
C:\Windows\System32\runas.exe /netonly /user:user@domain.local "mmc %SystemRoot%\system32\adsiedit.msc"
C:\Windows\System32\runas.exe /netonly /user:user@domain.local "mmc %SystemRoot%\system32\domain.msc /server=pdc.domain.local"
Note: I’ve added an extra parameter to specify the PDC Emulator, otherwise you may receive the error “You cannot modify domain or trust information because a Primary Domain Controller (PDC) emulator cannot be contacted.”
C:\Windows\System32\runas.exe /netonly /user:user@domain.local "mmc %SystemRoot%\system32\dssite.msc /domain=domain.local"
Note: I’ve added an extra parameter to specify the domain, otherwise you may receive the error “Naming information cannot be located because: The specified domain either does not exist or could not be contacted.”
C:\Windows\System32\runas.exe /netonly /user:user@domain.local "mmc %SystemRoot%\system32\dsa.msc /domain=domain.local"
Note: I’ve added an extra parameter to specify the domain, otherwise you may receive the error “Naming information cannot be located because: The specified domain either does not exist or could not be contacted.”
Step 4 – Applying Run As Commands
Option 1: Run from an Elevated Command prompt
Right-click the command prompt (cmd.exe), select Run as Administrator, and enter one of the runas commands in the previous section.

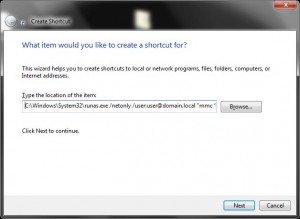
option 2: create shortcut and run as administrator
Right-click in the Windows file explorer, select New, click shortcut, for the location enter one of the runas commands from the previous section, click Next, name the shortcut appropriately, and click Finish. Whenever you launch the shortcut, right-click it and select Run as Administrator.
option 3: modify RSAT shortcuts
Under Administrative Tools on the start menu, right-click each RSAT shortcut, click Properties, and modify the target using the appropriate runas command from the previous section. Whenever you launch the shortcut, right-click it and select Run as Administrator.


24 comments
2 pings
Skip to comment form
You’re a god! Thank you very much!
Saved me a lot of troubles.
Thanks for the article, helped me greatly.
You are a star!! This has been bugging me for a while now and I could not work it out.
I jsut wanted to add I used the /savecerd command also so that you only have to input your password once.
C:\Windows\System32\runas.exe /user:user@domain.com /savecred “mmc %SystemRoot%\system32\dsa.msc”
Does this work with if UAC is enabled? I can’t seem to get it to work no matter what I do as even when I right-click and “Run As Administrator” I receive the “This command requires elevation” message. I have the “Default” UAC setting enabled currently.
Author
Yes this works with UAC enabled, which is how I run it myself. On Step 4 the three options there show how to run it with elevated privilege when using UAC.
Doesn’t seem to work on the latest RSAT for Windows 10. Cant get it to launch after I enter my password. Tried option 1 & 3. I can still launch ADUC if I right click & select run as a different user.
Author
RSAT for Windows 10 was just released on 8/19/2015 (just a few hours ago). Previous to that, RSAT tools that were compatible with Windows 10 Technical Previews didn’t work on the Windows 10 Full Release (Released 7/29/2015). If you’re running Windows 10, make sure you’ve upgraded to the full release and not any technical preview. Next install the latest RSAT tools:
https://www.microsoft.com/en-us/download/details.aspx?id=45520
I’ve just installed them myself and will do some testing… If I find any additional notes, I’ll update the article accordingly
Yes. I used the RSAT that was released yesterday. Got it to work but it opens a command prompt which closes once I close ADUC.
——–
runas /user:domain\username “cmd /c mmc.exe dsa.msc”
Author
I did some testing on my system and if you have UAC enabled, on options 2 and 3, you need to right-click the shortcut and click “Run as Administrator”. If you do not do that, the RSAT tools won’t open. You’re launching cmd with run as and having that launch mmc.exe. The command prompt will stay visible because that is what is running mmc.exe. I’ll update the directions by adding a note to run the shortcut as administrator which will fix your issue
So.. I have done everything listed above (cmd file – UAC off)….. I get Dsa to open.. I can move-disable-etc but I cannot rename PCs? Running Windows 10pro…
Funny part is that it works fine on my Win 8.1P machine.
hi
SooOOO helpful! Company makes us use a separate login for admin, so this is the work around I needed. Thanks!!
hi man.i’m from iran.and so looking for learning RSAT.and find this web site.you’re article really perfect and solved my problem. i wanna to give you so so thanks. god bless you.
Why go for all these hassles? Easiest way is Press CTRL+SHIFT right click on dsa.msc click on run as different user. FINISH
Author
Sumanthi,
I’ve posted this as a “complete solution” meaning, you do it once and that’s it. Yes you can do SHIFT + right-click to do a run-as (Not CTRL+SHIFT+Right-click as Lee beat me to), but if you have to open an RSAT tool multiple times, it much easier to do a simple click vs. shift plus click every time, every day, etc… Also, if you need to delegate permissions for AD to certain users/groups such as HR that need access to certain portions of AD, they are normally not the savviest of users and you can prevent yourself multiple calls by setting up their shortcut vs. expecting them to remember shift-right click every time they need to update a users title, etc.
Sumathi, you don’t need to press CTRL, just the SHIFT key when right clicking brings up the “run as different user”.
Author
Lee,
Thanks for the correction for anyone that might read that… I try to keep things 100% correct in my posts and comments to prevent any mis-information. I let that one slip by without correcting first!
Is there way for it not to ask for the password everytime?
Author
Yes, this same question was answered in the comments near the top. Basically, you can use the /savecred option with runas.exe
Wouldn’t this create a security concern, that running through the other account is trying to prevent? Say you open an email attachment you shouldn’t on your regular AD account and it becomes compromised…. Wouldn’t the /savecred option with runas.exe create a possible security risk to the elevated admin account?
Author
Yes, if they had a remote shell they could open the shortcut with the saved credentials and have access to your AD. Likewise if their malware was specifically looking for this exploit, it could as well although that is less likely to occur.
Personally, I wouldn’t suggest saving creds and never do
In Microsoft’s Active Directory, OUs do not confer access permissions, and objects placed within OUs are not automatically assigned access privileges based on their containing OU. This is a design limitation specific to Active Directory.
can this method use at services.msc logon account? i’m work on standalone server but some services need to get authenticate thought domain before it can start possible?
Thanks for your very nice Tutorial – i work great.
My Machine is a AzureAD registered machine and i connectet to my “old local domain” with your guid.
perhabs you could/should add these comand for connect DNS
C:\Windows\System32\runas.exe /netonly /user:\ “mmc %SystemRoot%\system32\dnsmgmt.msc [/DC1.DOMAIN.LOCAL]”
[…] This will ask you for the Administrator password and log you in accordingly. It may be necessary, once the management console is started up, to re-select domain controller and type in the name or ip-address of your domain controller. For more names of snap-ins, refer to this excellent resource […]
[…] Run Active Directory Management Tools as Another User … […]