If you’ve ever received an error connecting to a L2TP endpoint from a Windows client, where the L2TP endpoint or Windows client is behind a NAT-T device (Or Double NAT), it is most likely due to the Windows client not supporting Internet Protocol security (IPsec) network address translation (NAT) Traversal (NAT-T) security associations to servers that are located behind a NAT device. In my specific case, I setup an L2TP connection on an Ubiquiti Edge Router ER-4 that was behind a double NAT on the WAN. On the Windows client, you would most likely receive an error similar to:
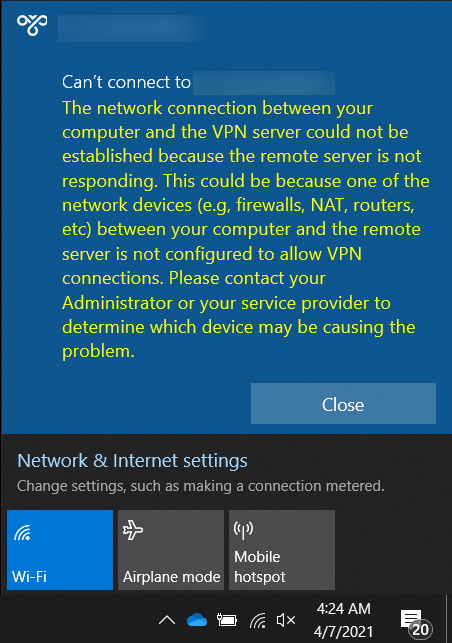
The network connection between your computer and the VPN server could net be established because the remote server is not responding. This could be because one of the network devices (e.g., firewalls, NAT, routers, etc.) between your computer and the remote server is not configured to allow VPN connections. Please contact your Administrator or your service provider to determine which devices may be causing the problem.
Sources
- https://community.ui.com/questions/EdgeMax-L2TP-with-Double-NAT/e4d45aa3-bb25-4402-97ba-b3b86877499c
- https://docs.microsoft.com/en-us/troubleshoot/windows-server/networking/configure-l2tp-ipsec-server-behind-nat-t-device
- https://help.ui.com/hc/en-us/articles/204950294-EdgeRouter-L2TP-IPsec-VPN-Server
By default, Windows Vista and Windows Server 2008 don’t support Internet Protocol security (IPsec) network address translation (NAT) Traversal (NAT-T) security associations to servers that are located behind a NAT device. If the virtual private network (VPN) server is behind a NAT device, a Windows Vista or Windows Server 2008-based VPN client computer can’t make a Layer 2 Tunneling Protocol (L2TP)/IPsec connection to the VPN server. This scenario includes VPN servers that are running Windows Server 2008 and Windows Server 2003.
Explanation
Because of the way in which NAT devices translate network traffic, you may experience unexpected results in the following scenario:
- You put a server behind a NAT device.
- You use an IPsec NAT-T environment.
If you must use IPsec for communication, use public IP addresses for all servers that you can connect to from the Internet. If you must put a server behind a NAT device, and then use an IPsec NAT-T environment, you can enable communication by changing a registry value on the VPN client computer and the VPN server.
Resolution
To create and configure the AssumeUDPEncapsulationContextOnSendRule registry value, follow these steps:
- Log on to the Windows Vista client computer as a user who is a member of the Administrators group.
- Select Start > All Programs > Accessories > Run, type regedit, and then select OK. If the User Account Control dialog box is displayed on the screen and prompts you to elevate your administrator token, select Continue.
- Locate and then select the following registry
- subkey:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\PolicyAgent
- subkey:
- On the Edit menu, point to New, and then select DWORD (32-bit) Value.
- Type AssumeUDPEncapsulationContextOnSendRule, and then press ENTER.
- Right-click AssumeUDPEncapsulationContextOnSendRule, and then select Modify.
- In the Value Data box, type one of the following values:
- 0It’s the default value. When it’s set to 0, Windows can’t establish security associations with servers located behind NAT devices.
- 1When it’s set to 1, Windows can establish security associations with servers that are located behind NAT devices.
- 2When it’s set to 2, Windows can establish security associations when both the server and VPN client computer (Windows Vista or Windows Server 2008-based) are behind NAT devices.
- Select OK, and then exit Registry Editor.
- Restart the computer.
